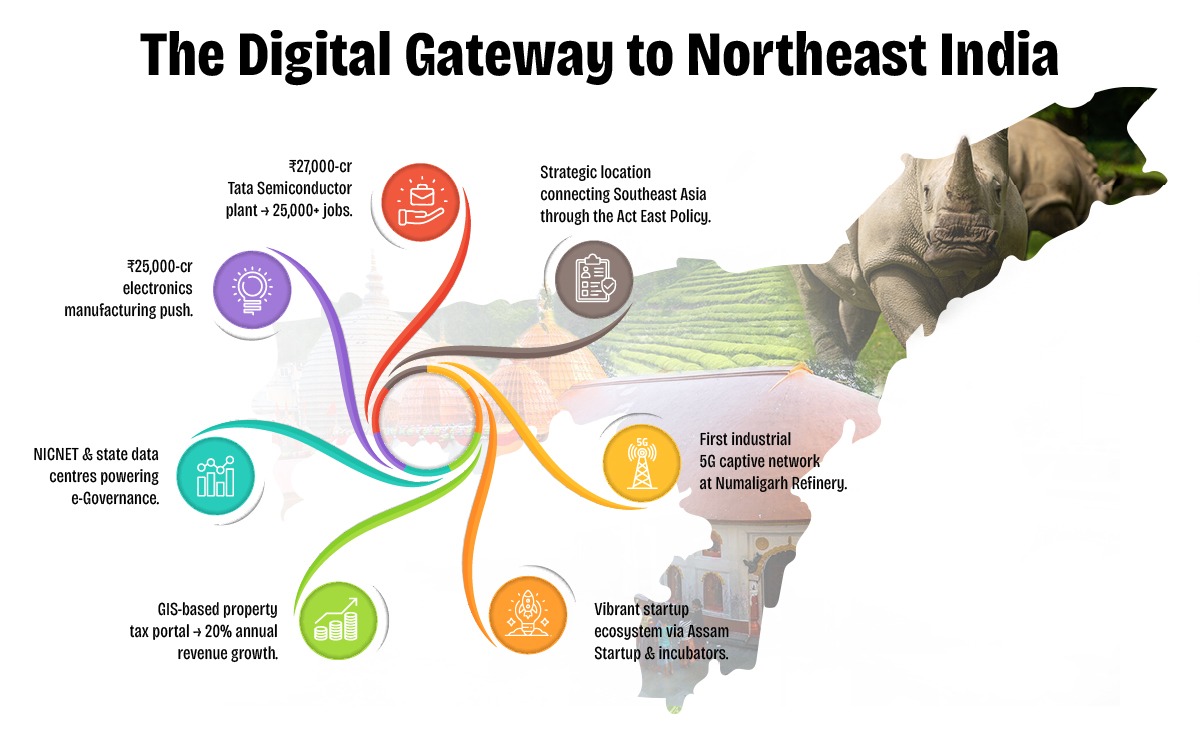
Assam is rapidly emerging as a digital innovation hub in Northeast India, driven by visionary policies and proactive governance under the Digital Assam initiative. With a growing IT ecosystem, expanding digital infrastructure, and a strong focus on e-Governance, the state is positioning itself at the forefront of India's digital transformation.
To further accelerate this journey, Elets Technomedia, in collaboration with the Information Technology Department, Government of Assam, is organising the National Digital Innovation Summit 2025 on 5-6 December in Guwahati. The summit will provide a platform for policymakers, industry leaders, innovators, and technologists to deliberate on strategies to advance the state's digital progress.

Sessions

Dynamic Speakers

of Special eGov Magazine

featuring cutting-edge solutions

Networking
An Initiative By

Knowledge Partner

Host Partner

Supporting Partner

Powered By

Banking Partner

Gold Partners


Digital Transformation Partner

Secured Communications Technology Partner

Associate Banking Partner
Technology Partner

Data Center Partner

E-Governance Partner

Branding Partners




Supporting Partners



Based on technical breakdowns from sandbox environments like VirusTotal and Hybrid Analysis, the contents of this archive (and its various versions) are known for:
Frequently re-uploaded to sites like Mega.nz or MediaFire after being taken down for TOS violations. Safety Recommendation
(e.g., 4chan, 2ch) where it is posted to "troll" users looking for niche content.
If you have already downloaded it, delete it immediately without opening the archive. If you have executed any files from within the RAR: Disconnect from the internet to prevent data exfiltration.
The malware often attempts to hide itself by injecting code into legitimate system processes like explorer.exe or svchost.exe .
Some variants include "stealers" that target browser cookies, passwords, and cryptocurrency wallets.
Distributed via direct message or in community channels under the guise of a "leaked" game or asset pack.
Digital Transformation in Governance
Startups, Innovations & Entrepreneurial Growth in Northeast India
Artificial Intelligence (AI) for Inclusive Growth
Cloud, Data & Cybersecurity for a Secure Digital Future
Digital Infrastructure & Connectivity in Northeast India
Skilling, Capacity Building & Future Workforce Development
E-Governance & Citizen-Centric Service Delivery
Based on technical breakdowns from sandbox environments like VirusTotal and Hybrid Analysis, the contents of this archive (and its various versions) are known for:
Frequently re-uploaded to sites like Mega.nz or MediaFire after being taken down for TOS violations. Safety Recommendation
(e.g., 4chan, 2ch) where it is posted to "troll" users looking for niche content.
If you have already downloaded it, delete it immediately without opening the archive. If you have executed any files from within the RAR: Disconnect from the internet to prevent data exfiltration.
The malware often attempts to hide itself by injecting code into legitimate system processes like explorer.exe or svchost.exe .
Some variants include "stealers" that target browser cookies, passwords, and cryptocurrency wallets.
Distributed via direct message or in community channels under the guise of a "leaked" game or asset pack.













































& many more...
Ritika Srivastava
+91- 9990108973Anuj Sharma
+91- 8860651650