Samsung A260G U1 Android Oreo 8.1 Root File?q=Samsung A260G U1 Android Oreo 8.1 Root File
Samsung A260G U1 Android Oreo 8.1 Root File?q=Samsung A260G U1 Android Oreo 8.1 Root File
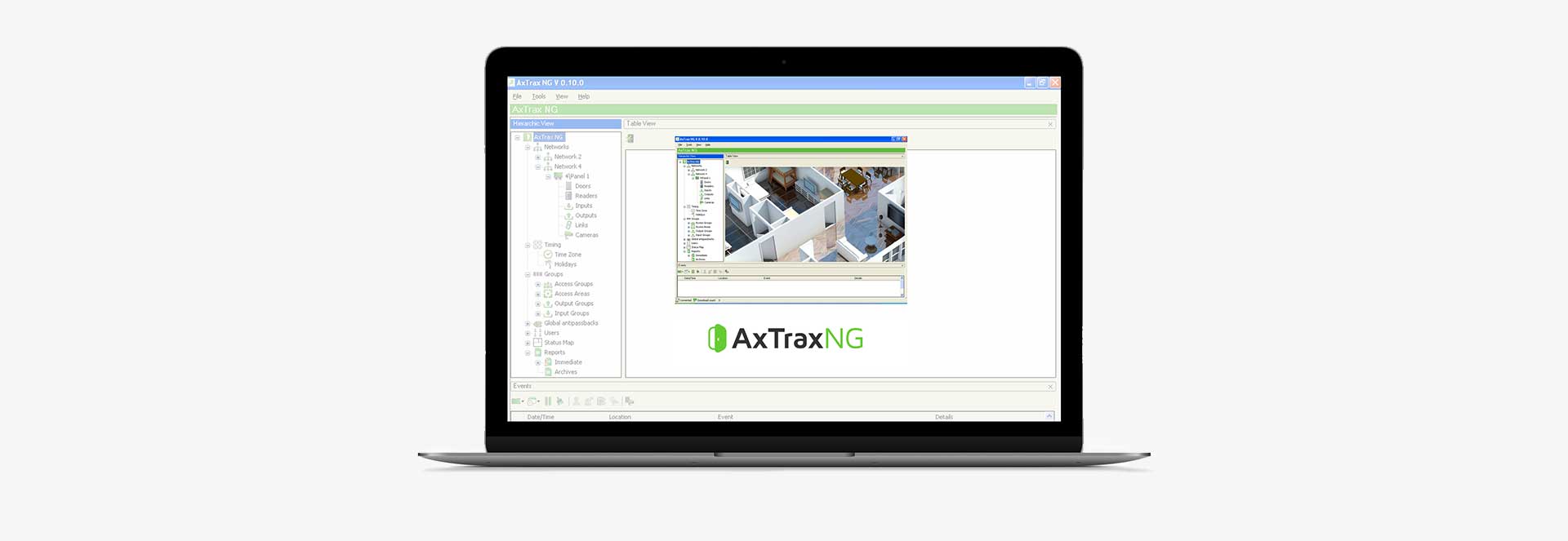
AxTraxNG Software
AxTraxNG is a complete server-client software management that enables setting physical access control policy across organizations that is available in multiple languages and date formats. The server manages thousands of networked access control panels and system users. The user-friendly interface is intuitive, reliable and rich in
functionality. With Rosslare’s SDK tool AxTraxNG also leverages easy integration and deployment of various
applications in security, safety, time and attendance and more. AxTraxNG allows the control and monitoring of
every aspect of site access.
Product Datasheets Development Tool
Samsung A260g U1 Android Oreo 8.1 Root File?q=samsung A260g U1 Android Oreo 8.1 Root File May 2026
Globally market-proven software with tens of thousands of
installations
Sophisticated feature set that is easy to manage, install and use
Constantly improved and updated, continuous support and
development
Fully scalable, enabling implementation of projects from a single to
thousands access points
Easy integration with any third-party software and tools using dedicated SDK
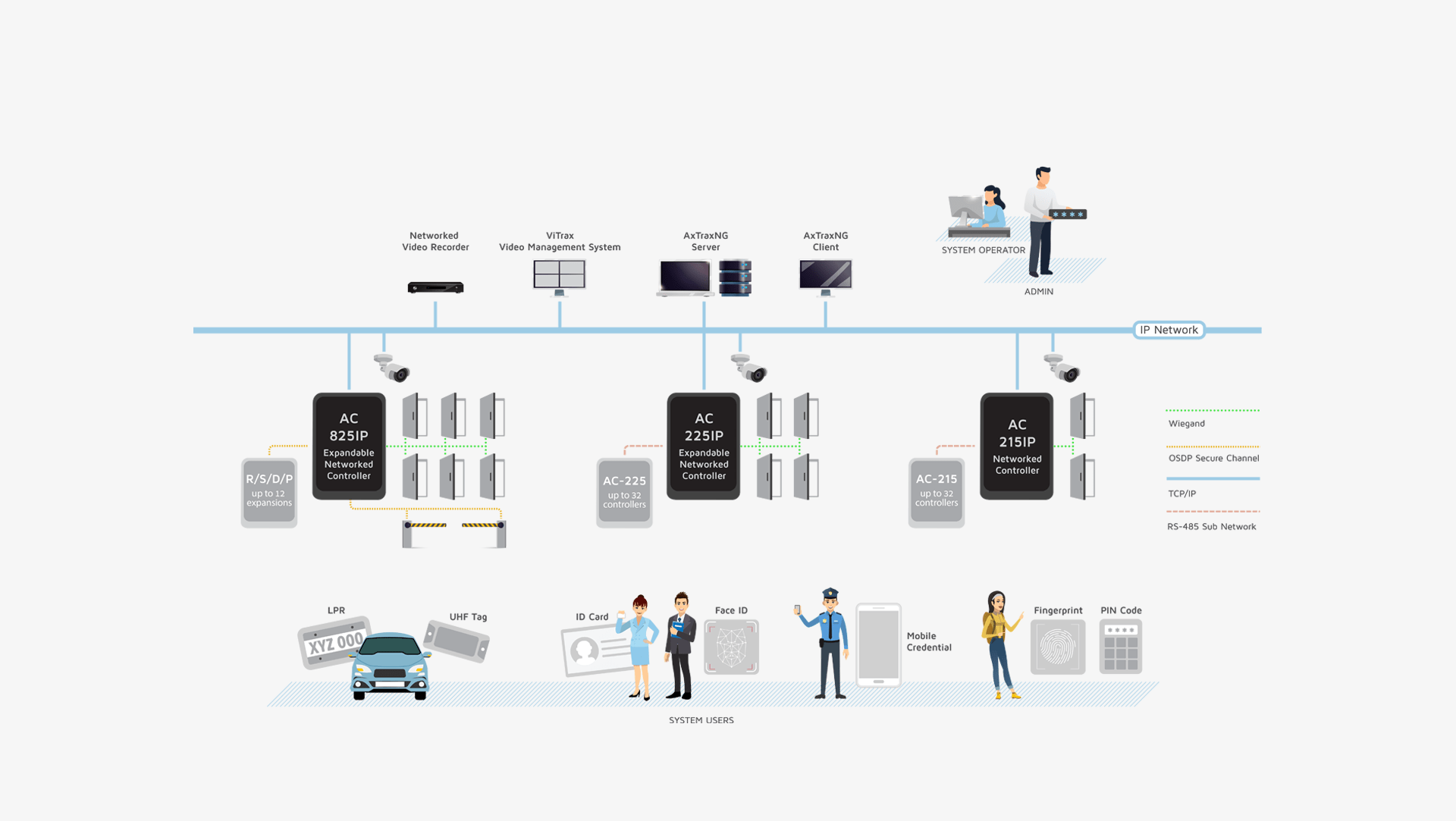
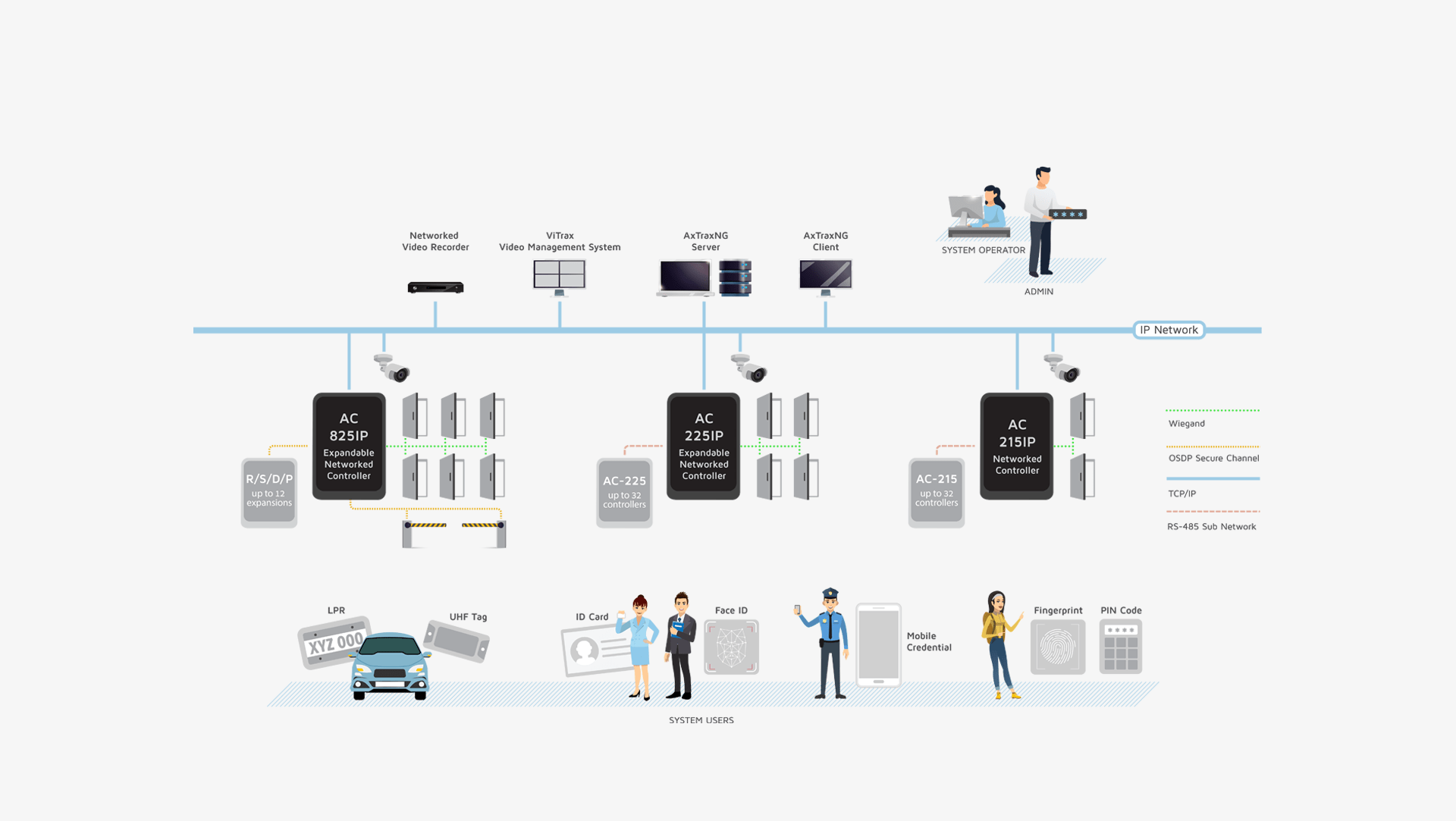
You can choose from a range of Rosslare Control Panels and Expansions
Samsung A260g U1 Android Oreo 8.1 Root File?q=samsung A260g U1 Android Oreo 8.1 Root File May 2026

Samsung A260g U1 Android Oreo 8.1 Root File?q=samsung A260g U1 Android Oreo 8.1 Root File May 2026
Samsung A260g U1 Android Oreo 8.1 Root File?q=samsung A260g U1 Android Oreo 8.1 Root File May 2026
Rich System and Hardware Management Options, Access Control Policy (Business Logic), System Maintenance,
Integrations and Special features
Identity Management of users,
information fields, photo, access
credentials and user related access policies, from a central server with multiple Workstations (Clients)
Support for different types of user
credentials Including Face-ID,
Fingerprint, PIN-Codes, RFID, UHF Tags, NFC-ID, BLE-ID and LPR for vehicles
Production and export of reports from acquired data, Alarm management for operator workflow and a Rules based Automations Engine
Built-in software security with
encrypted database protects all
private user personal data, access policy rules and logged events for
a secure audit trail
Video integration with Rosslare’s Vitrax VMS and with Hikvision and Dahua NVR for access event-based video pop-up and photo snapshot reports
Samsung A260g U1 Android Oreo 8.1 Root File?q=samsung A260g U1 Android Oreo 8.1 Root File May 2026
Samsung A260g U1 Android Oreo 8.1 Root File?q=samsung A260g U1 Android Oreo 8.1 Root File May 2026
Samsung A260g U1 Android Oreo 8.1 Root File?q=samsung A260g U1 Android Oreo 8.1 Root File May 2026
: Offers a dedicated A260G U1 ROOT (A260GDDU1ASCH) file that was recently updated in October 2024.
: Features a downloadable ROOT A260G U1 8.1.0_Root .tar file specifically for this model. Manual Rooting Method (Recommended)
Several specialized repositories provide pre-prepared root files for this specific model and binary:
To root your running Android 8.1.0 Oreo with U1 (Binary 1) firmware, you can use specialized "root files" (pre-patched boot images) or manually patch your own firmware using Magisk. Direct Root Files (Binary 1 / U1)
We use cookies to ensure that we give you the best experience on our website. You must accept cookies in order to use this websites features. (Learn more on our Privacy Policy)
x